Rugged tablets—not your off-the-shelf product (COTS)—but handheld computers that are versatile, powerful, tough, and portable. Ruggedize, military-grade tablets are often found in healthcare, agriculture, manufacturing, logistics, construction, and utilities.
In warehouse management, rugged tablets offer a more flexible and reliable solution, with lower failure rates compared to nonrugged devices. They are especially appealing as IoT technology enables sensor-equipped devices to optimize warehouse operations and asset management.
In the automotive industry, rugged tablets play a crucial role in car repair shops, enhancing efficiency and streamlining various processes. Mechanics and technicians use these robust devices to access vehicle diagnostic software, enabling them to quickly identify and troubleshoot issues. Rugged tablets also facilitate communication with the central database, allowing real-time access to repair manuals, technical information, and parts inventories. They aid in documenting and tracking repairs, ensuring accurate records and reducing paperwork.

Additionally, rugged tablets enable seamless communication between mechanics and service advisors, enhancing customer service and reducing wait times. The durability and resistance to dust, liquids, and shocks make rugged tablets ideal for the demanding environment of car repair shops, empowering technicians with the necessary tools to expedite repairs and provide reliable services to customers. (Do you need a tablet that is resistant to hot temperatures and moisture? Estone can customize that for you.)
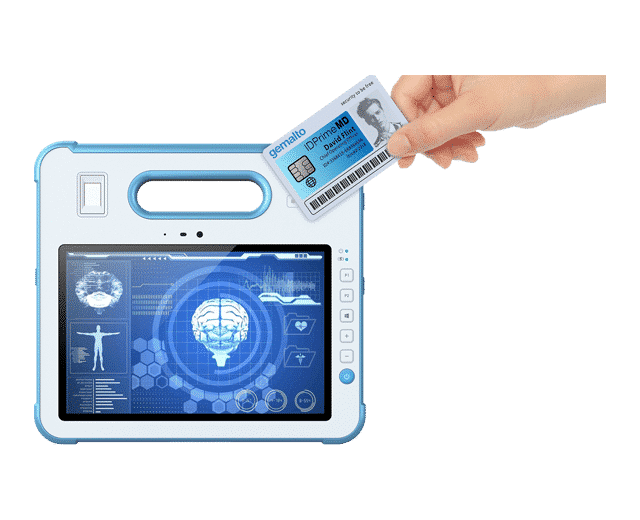
RFID Integration for Ultimate Security
With so many applications for rugged tablets, it becomes clear that access and security need to be integrated in case these devices get into the wrong hands.
In the RFID industry, a smart card refers to a type of card that incorporates both a traditional plastic card and an embedded microchip. This microchip, often referred to as an integrated circuit (IC) or chip, is capable of storing and processing data. Smart cards used in the RFID context are equipped with RFID technology, which allows them to communicate wirelessly with RFID readers.
When a user presents an RFID smart card near the reader, the reader emits a radio frequency signal. The RFID smart card contains a small, embedded chip and antenna that receives this signal and responds by transmitting its stored information back to the reader. The reader then decodes and processes the data, allowing it to authenticate the cardholder’s identity or grant access based on the provided information. This contactless communication enables quick and efficient interactions, making RFID smart card readers suitable for various applications, from access control to payment systems.
RFID card readers provide a convenient and efficient method of authentication and access control. By using RFID technology, these readers can quickly and accurately verify the identity of individuals through unique card credentials, reducing the risk of unauthorized access.
Having a built-in, integrated RFID reader versus an external USB attachment will allow for a seamless user experience that’s clear from physical obstruction that can hinder productivity.
RFID Systems
There are two methods to operate an RFID system, and multiple types of RFID readers and tags are available for use in the system. In an active system, the tags are continuously powered, emitting a radio signal like a beacon. On the other hand, passive systems do not power the tag until the reader sends energy to activate it for reading.
These systems utilize different frequency ranges, categorized as Low Frequency (LF), High Frequency (HF), Ultra-high Frequency (UHF), and Near Field Communication (NFC). The frequency ranges for each classification are as follows:
• LF: 125 KHz to 150 KHz
• HF: 3 MHz to 30 MHz (NFC: 13.56 MHz)
• UHF: 433MHz, 860 MHZ to 960 MHz
Enhancing RFID Card Reader Security
Secure Access Modules (SAMs) can significantly enhance RFID card reader security by providing a dedicated hardware platform for cryptographic operations and secure key management. SAMs store cryptographic keys used for authentication and encryption, preventing unauthorized access to sensitive data. When an RFID card is presented for authentication, the card reader interacts with the SAM to perform mutual authentication with the RFID card, ensuring that both parties are genuine. SAMs add an extra layer of protection, making it extremely difficult for attackers to extract cryptographic keys or manipulate data during communication. They also facilitate secure messaging between the RFID media, card reader, and the host system, ensuring that data transferred over the radio link remains protected. Moreover, SAMs can be updated remotely with firmware and configuration updates, enabling continuous security improvements without compromising sensitive information.
Estone Technology: ODM Customization for Rugged Tablets
Have a tablet design that needs integrated RFID? Estone can add or remove mission critical features such as RFID, barcode readers, WiFi, TPM security modules, 4G LTE wireless connectivity, GPS (GLONASS/BAIDOU), MSR card readers, light/thermal/gravity sensors, and more. We would love to hear how we can manufacture your product to your specific requirements. Contact us to learn more.
Looking for a rugged tablet with RFID capabilities? Check out our 8″ Ultra-Rugged Android Tablet, great for medical and retail sectors.
Sources:
Samsung.com
rfidjournal.com
techtarget.com
Designworldonline.com
openai.com
